Automate user management with user provisioning
Learn how to set up user provisioning to manage users in your SafetyCulture organization.
User provisioning connects your identity provider (IdP) to SafetyCulture so that user accounts are created, updated, and deactivated automatically. This page explains the two supported methods, SCIM and JIT, and covers requirements, setup, seat type configuration, and what gets synced.
The Microsoft Gallery app currently doesn't support SCIM. If your organization uses Azure Active Directory for single sign-on and you want to set up SCIM user provisioning, use a non-Gallery app for Active Directory instead.
Provisioning methods
SafetyCulture supports two methods of user provisioning: System for Cross-domain Identity Management (SCIM) and Just-in-Time (JIT).
| SCIM | JIT | |
|---|---|---|
| How it works | Continuously syncs users from your IdP to SafetyCulture | Syncs user data on each successful login attempt |
| Supported seat types | Full, lite, and guest | Full seat only |
| Automatic seat purchasing | Supported (Early Access) | Supported (Early Access) |
| Deactivating users | Automated via IdP | Manually via the web app |
| Removing users | Automated via IdP | Please contact our customer support team for assistance. |
| Group management | Supported | Not supported |
| Recommended for | Organizations that need full lifecycle management | Organizations that need simple, login-triggered provisioning |
Use SCIM if you need to manage the full user lifecycle, including deactivation, removal, and group membership, directly from your IdP. Use JIT if your organization only needs accounts created at login and does not require deactivation or group sync.
Support for single sign-on and user provisioningOur customer support team can only provide limited help for single sign-on and user provisioning. If your organization is on the Enterprise Plan, please contact your customer success manager for assistance.
Requirements
- SafetyCulture Premium Plan or Enterprise Plan
- Web app
- Single sign-on with SafetyCulture
- API token
- "Platform management: Organization" permission
Set up SCIM user provisioning
SafetyCulture supports all identity providers for SCIM provisioning. Setup steps vary depending on your chosen identity provider. Use the following guides for the most common providers:
During setup, your identity provider will ask for an API token and the following connection details:
- Connector URL:
https://api.safetyculture.com/accounts/scim/v2 - Unique Identifier: Each user's email address.
- Authorization: HTTP Header (Bearer token)
Set up Just-in-Time (JIT) user provisioning
- Log in to the web app.
- Click your organization name on the lower-left corner of the page and select Organization settings.
- Select Security on the top of the page.
- Click Edit in the "Single sign-on (SSO)" box.
- Turn "Just-in-Time provisioning (JIT)" on.
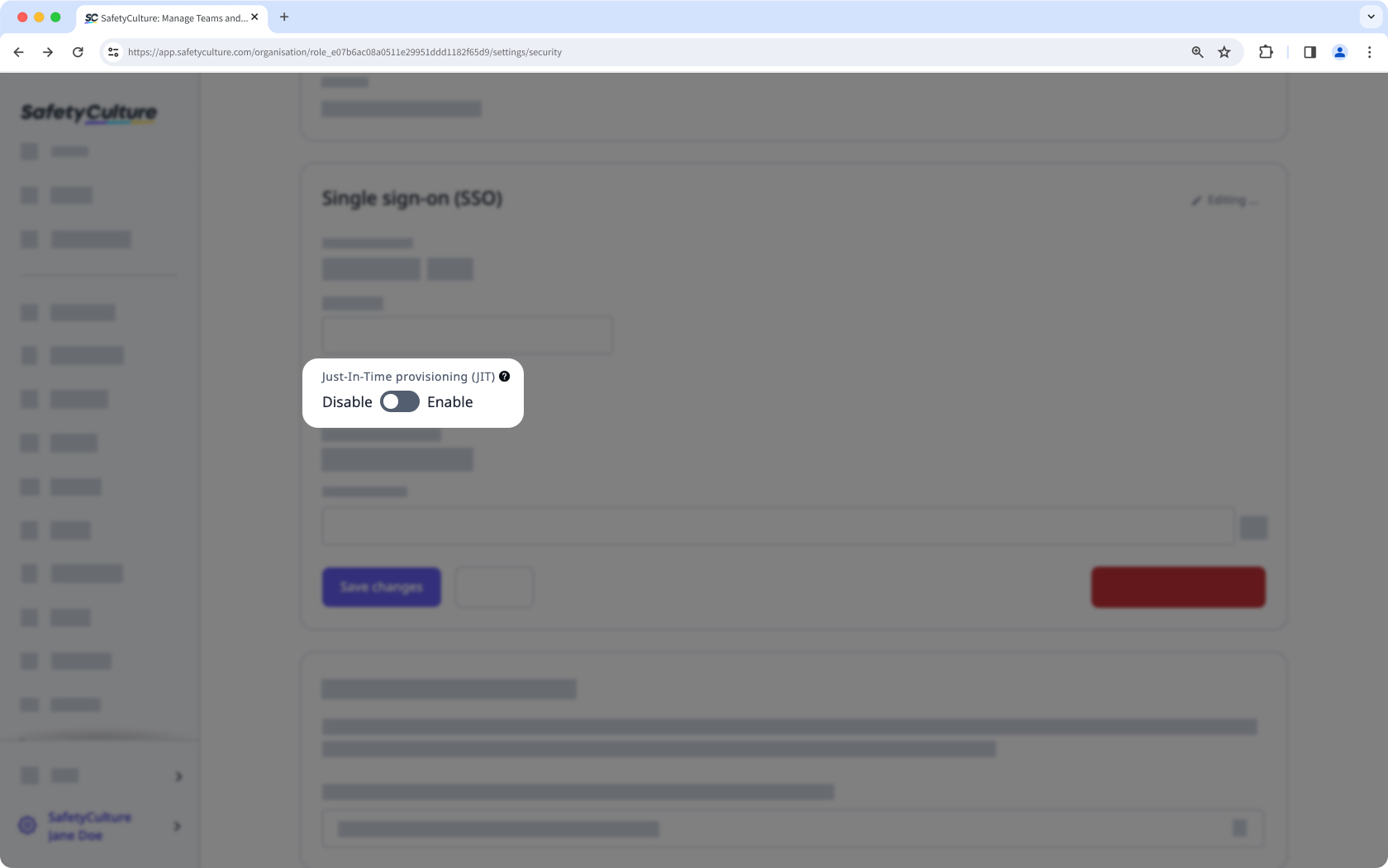
- Click Save changes.
- For each email domain, click Verify and follow the instructions in the pop-up window to update your DNS records. Then, click Verify.
Setting up JIT with Azure Active DirectoryIf your organization uses Azure Active Directory for single sign-on, and you want to set up JIT user provisioning, refer to Microsoft's support article for instructions.
Manage seat types for provisioned users
Newly provisioned users are assigned a full seat by default. You can change this by configuring seat type mapping in your identity provider before provisioning runs.
Configure seat type mapping
-
In your identity provider, open the attribute mapping settings for your SafetyCulture application.
-
Map the seat type attribute using the notation for your identity provider:
-
Microsoft Entra ID (Azure AD):
- External namespace:
seat_typeurn:ietf:params:scim:schemas:extension:safetyculture:2.0:seat_type`
- External namespace:
-
Okta:
- External name:
seat_type - External namespace:
urn:ietf:params:scim:schemas:extension:safetyculture:2.0
- External name:
-
-
Set the value to one of the following options:
full: full seat (default if no value is set)lite: lite seatfree: guest seat
-
Save your mapping and test provisioning with a single user before turning on auto-sync.
Seat availability and billing
This feature is currently in Early Access. If your organization is enrolled, SafetyCulture automatically purchases additional paid seats when your seat limit is reached during user provisioning.
- Users are provisioned with the correct seat type.
- Your billing admin receives a summary email for any paid seats purchased automatically.
- Your next invoice will include a prorated charge for the seats purchased from the date they were added.
Monitor your seat allocation regularly in the SafetyCulture web app to stay on top of your plan. Contact your customer success manager if you have any questions.
Synced data
The following data is synced with your identity provider for each user:
- Name
- Email address
- Group names
- Group members (for each group)
SCIM provisioning also supports deactivating and removing users or groups. JIT only supports creating and updating users.
Frequently asked questions
What happens if a user already has a SafetyCulture account?
They'll be added to your organization like any other user. Being a part of multiple organizations just means that they can switch between your organization and others.
How do users log in after they've been provisioned a SafetyCulture account?
Users added through user provisioning will not have a password set by default. However, they can still log in via single sign-on, a one-time email code received via email, or by creating a password using a password reset email, if passwords are enabled for your organization.
Updated 3 months ago